Hanbiro IPS Outline
Hanbiro will introduce the IPS for Self-developed DDoS.
Features
Traffic and Packet Tracking Table
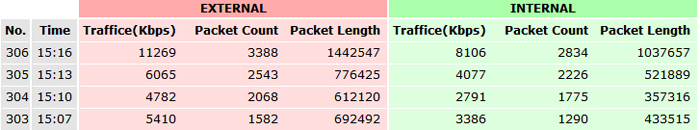
Check the amount of traffic packets, packet total length every three minutes
By clicking on the line of time, the following table will be shown.
Detailed analysis table of packets
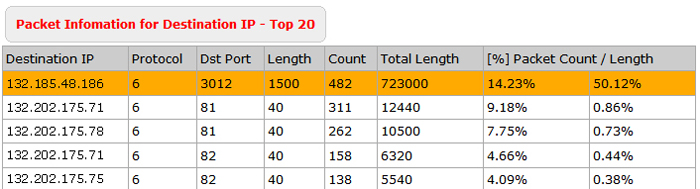
You can see IP, protocol, port, packet length, packet count, and packets percent by type of packet.
Length of the packet or count displays at least 20% of the packets in orange.
When attacks occur, the attack targeted IP and what type of attack packets can be determined.
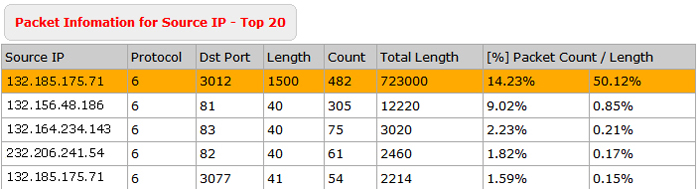
If you click on a specific IP, detailed analysis of the sent and received packet of the destination IP is shown as below.
Detailed profiles by IP
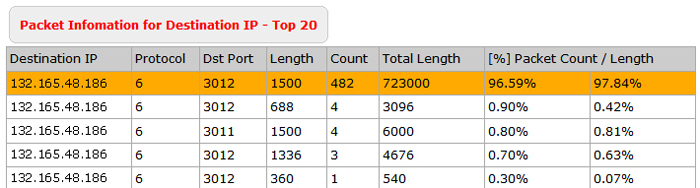
It is possible to check packet count and traffic generated in destination IP, and what type of packet flows happened to a specific server.
Real-time packet status
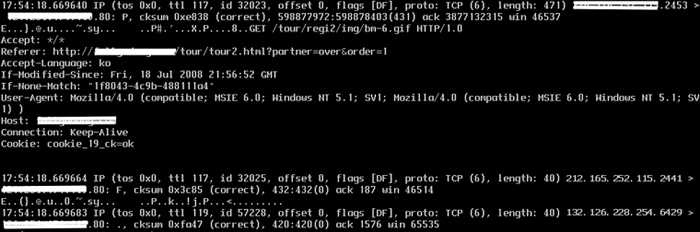
The immediate and effective defense against attacks is available though a detailed analysis of the attack packets and real-time analysis of the flow type of the packet.